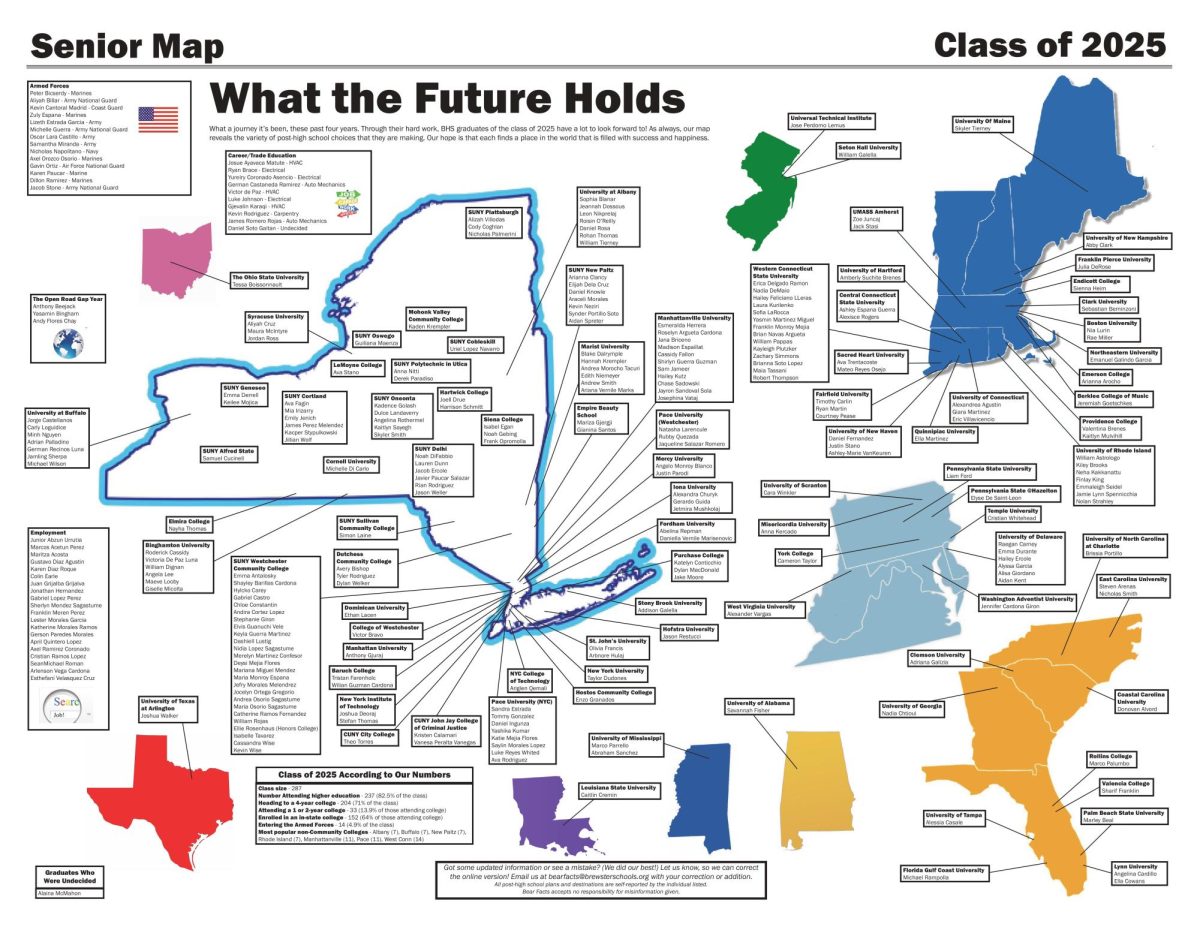
How Safe is our School, Really?
May 11, 2018
Is our school as safe as we think and hope it is? Here’s your chance to decide for yourself. Back in 2013, Homeland Security issued a list of recommendations for schools to use as guidelines for keeping their school safe. Take a look at their guidelines and see how we measure up.
ACCESS CONTROL
- The facility limits building access points.
- Designated access points are monitored to control facility access.
- Signs direct visitors to designated building entrances and exits. (See photo in slideshow)
- Exterior doors to gyms, maintenance areas, kitchen, and delivery areas are secured when not in use.
- Visitors are required to check in with the front office upon arrival and departure.
- Visitors are provided with school issued identification badges when on school grounds.
- Policies are in place for those with and without appointments or official school business.
- Vendors and contractor personnel are escorted throughout the facility.
- A key control program is established that monitors keys, entry cards, and duplicates.
- Key control program is audited annually.
BUILDING EXTERIOR
- Policies are in place that restrict access to bus-loading zones.
- Bus-loading, unloading, drop off zones and fire zones are clearly marked.
- School designates areas for use of parking lots (e.g., staff lot, student lot, visitor spaces).
- Parking system incorporates an identification system (e.g., placards in windshields).
- Appropriate perimeter barriers or gates are installed and secured when not in use.
- Windows are locked securely.
- Window hardware and frames are regularly inspected for security weaknesses.
- Facility has visual surveillance capability (e.g., designated surveillance points, cleared lines of sight).
- Clear zones adjacent to buildings are free of vegetation and other obstructions.
- Barriers are installed to protect doors and windows from small arms fire and explosive blast effects.
- School grounds are adequately lit.
- Vandalism and graffiti is documented and removed.
- Mechanical, electrical, and other equipment are surrounded by protective enclosures to prevent unauthorized access.
- Access to the roof is restricted. (See photo in slideshow)
- Speed limits are posted.
BUILDING INTERIOR
- School front office is clearly marked.
- First aid/school nurse office location is clearly marked.
- Critical utility systems and equipment are secured and locked.
- A positive inventory is kept on chemicals in use or used in science classes or laboratory areas.
- Custodial and storage closets are secured and locked.
- The number of containers and trashcans in hallways, atriums, and lobby areas are minimized.
- Unassigned lockers are secured.
- Doors and stairwells are numbered.
- Stairwells, hallways, and restrooms are adequately lit.
- Smoke detectors have vandal-resistant features (e.g., tamper alarms or protective cages). (See photo in slideshow)
- Doors and locks are in good condition.
- Easy access to fire extinguishers.
- Adequate access to first aid supplies (e.g., automated external defibrillators (AEDs)).
- Blast fragment retention film is on windows.
- Security information and training includes training on how to identify suspicious packages.
- Faculty and staff have been trained to appropriately respond to and report threatening/suspicious phone calls.
- School maintains, reviews, and updates a code of conduct/school handbook. (See photo in slideshow)
- Students do not have access to the school without direct staff supervision.
- Curricula and programs aimed at preventing harmful behaviors are implemented (e.g., social problem-solving, life skills, anti-bullying, mentoring programs, character education).
- Photo identification badges are issued to all faculty, students, and staff.
COMMUNICATION SYSTEM
- Systems are installed that provide two- way communication between faculty, staff, administrators, and security personnel.
- Communication system is installed that provides communication with all people at the school, including faculty, students, staff, emergency response teams, and visitors.
- A notification protocol is developed that outlines who should be contacted in emergencies and how. (See photo in slideshow)
REPORTING PROCEDURES
- School has a single point of contact for reporting threats, threatening behavior, or concerning behavior and is available 24/7.
- There are multiple ways someone can reach the point of contact for reporting potential threats (e.g., email, telephone, online, in-person).
- Reporting can be anonymous.
- There are clear policies in place for collecting and acting on information about a threatening or potentially threatening situation.
- Policies explain how information will be handled confidentially and appropriately.
SECURITY EQUIPMENT
- Security camera tapes or recordings are retained for an allotted time period.
- All emergency response equipment and supplies are checked on a regular basis.
SECURITY PERSONNEL
- A school security director is designated to develop, implement, and coordinate all security-related activities.
- School security personnel include an armed trained police officer or school resource officer.
- School security personnel are stationed at a single school.
- School security personnel are a visible and regular presence during school hours of operation.
- School security personnel are deployed during normal school hours of operation and special events.
- Security personnel check for unauthorized vehicles in parking lots or on school grounds.
- Halls, common areas, and gyms are monitored for suspicious items (e.g., backpacks, briefcases, boxes).
- Security personnel are deployed to assigned areas to regularly inspect sensitive or critical areas (e.g., auditoriums or under stages where items such as weapons or explosive materials can be hidden).
- Faculty and staff monitor hallways, stairwells, and restrooms during school hours.
- If the building is used after school hours, security personnel are present.
CYBERSECURITY
- School maintains a well-trained computer security staff.
- School faculty and staff are required to use passwords and unique login information to access electronic files.
- Security plans for computer and information systems are established.
- Faculty, staff, and students are trained in safe and secure computer use.
- Cybersafety and cyberbullying programs are provided for students.
- Video security system is adequately protected against hackers.
EMERGENCY OPERATIONS PLAN
- A comprehensive school emergency operations plan has been developed.
- Plan takes into consideration numerous circumstances and criteria for response (e.g., lockdown, evacuation, shelter-in-place). (See photo in slideshow)
- Plan contains an updated map of the school’s floor plan that includes room numbers, evacuation routes, and utility shut offs.
- Plan contains directions that provide for the needs of students, staff, and visitors with disabilities and other functional and access needs.
- Plain contains action checklists for teachers, administrative staff, and other staff located throughout the school to follow during incident response.
- Plan includes components for post-incident response/recovery (e.g., stress management, mental health services, infrastructure restoration, post-incident evaluation, business continuity plans etc.)
School conducts regular exercises/drills of emergency plans.